Effective access to beneficial ownership information
Designing access regimes
Debates around access to BO information have centred around whether or not information should be made available to the public, or to which parties beyond governments. However, while who has access to information is critical, this should not replace considerations of what information users should have access to, and how they might access and use such data. Designing an effective access regime will raise both legal and technical questions. Therefore, setting up multi-disciplinary teams covering policy, legal, and technical angles will help to ensure each element is comprehensively addressed.
At the centre of ensuring effective, responsible, and sustainable access to BO information for legal vehicles is the creation of different layers with distinct characteristics (for a graphical representation of layered access, see Figure 2). Most access regimes have at least two layers. This includes a layer with access to most or all of the information collected or gathered as part of BO disclosure, generally for authorities legally mandated to handle matters related to a jurisdiction’s BOT policy objectives (e.g. competent authorities, in the case of AML). Additional layers may exist for specific user groups and the public, which may vary the ways in which the information can be used (see Box 8).
The following section outlines key considerations in designing different layers in an access regime with data usability at its core, and considers privacy and data protection in this process. These considerations are equally relevant for the development of new access regimes and iterative improvements to existing ones.
Assessing the context
Implementing agencies should take stock of their context by:
- clarifying the purpose of reforms;
- reviewing relevant legal frameworks and international standards; and
- identifying users and understanding their needs.
Clarifying the purpose of reforms
Clearly defining the policy goals of BOT reforms from the outset is fundamental to informing subsequent decisions about laws, policies, and systems. A narrow purpose, such as AML, may make it easier to build quick, broad political support for reforms. However, this may require the development of laws and systems to cater to different purposes at a later stage, which could be difficult or expensive to alter. Limiting the use of BO information to a specific purpose risks constraining the wide-reaching impact that BOT can have on various policy goals. Therefore, implementing agencies and policymakers should carefully consider the range of goals that may be relevant at an early stage.
Some jurisdictions have anchored their reforms in a broader purpose, which provides opportunities to use BO information to address a range of interconnected issues. For example, Canada’s objectives for BOT include to “prevent illicit activities, improve Canadians’ trust in corporate institutions and ensure a well-functioning marketplace”. [23] Similarly, the United Kingdom (UK) Overseas Territory (OT) of St Helena lists four broad purposes:
National security, anti-corruption, anti-money laundering, and preventing organised crime; Protecting individuals and business from fraud; Improving economic wellbeing by facilitating the growth of the digital, financial and professional service sectors; and, the UK Government has issued a draft order in council to all Overseas Territories to implement a Publicly Accessible Register of Beneficial Ownership (PARBO). St Helena Government (SHG) recognises the value in complying with the draft Order in Council. [24]
Impact assessments and consultations with implementing agencies, potential users, and businesses providing the information will help identify, refine, and clarify the purpose of reforms. These processes will also help identify parties that have a role to play in the effective implementation of BOT reforms, including the key users of a BO register. Namely, those who will:
1. disclose information (e.g. businesses);
2. administer the data (e.g. the business registrar);
3. use the data (e.g. other government agencies, banks, and civil society).
Whatever the outcome of these assessments and consultations, the purpose of the reform and a legal basis for collecting and processing the information will need to be clearly stated in legislation or associated policy documents. [25]
Reviewing relevant legal frameworks and international standards
Assessing a country’s obligations and requirements under national and international legal and policy frameworks can typically inform the design of access regimes in BOT reforms.
Requirements around access provisions
Domestic legal frameworks may require access by specific groups of users to certain information. For example, the Philippines New Government Procurement Act 2023 and Kenya’s Executive Order 2018 require information about certain companies involved in public procurement to be available to the public. [26]
Compliance with international standards may also require or encourage considering access for various user groups. For example, the Financial Action Task Force (FATF) requires timely access to BO information by competent authorities and to public authorities over the course of public procurement, and recommends that governments should consider timely access by obliged entities. [27] The United Nations Convention against Corruption’s Resolution 10/6 also calls for access for procurement agencies. [28] The Global Forum’s Exchange of Information on Request for tax purposes requires access by competent authorities, and for those competent authorities to share this information upon request with counterparts. [29] The 2023 Extractive Industries Transparency Initiative (EITI) Standard requires certain information fields to be made available to the public. [30] Finally, the EU AMLD6 requires member states to implement specific access provisions for domestic authorities and obliged entities, as well as various categories of parties deemed to have a legitimate interest (see Box 8). [31]
Requirements around data protection and privacy
Legal contexts can vary significantly, and because of this there is no universal approach to balancing access and privacy. Implementing governments should therefore begin by taking stock of their contexts and obligations. This includes considering data protection and privacy rights as laid out in domestic and international instruments, including constitutions, data protection legislation, and human rights treaties or conventions. Data protection legislation or regulatory processes may also require governments to conduct privacy impact assessments to identify any data protection issues in relation to the various aspects of the reforms, including access to information. [32]
To illustrate, an African Union member state would need to consider the African Union Convention on Cyber Security and Personal Data Protection (Malabo Convention, 2014), while EU member states would need to consider the EU Charter of Fundamental Rights and the EU GDPR. The EU GDPR defines personal data as “any information […] related to an identified or identifiable natural person”. [33] This contrasts with the Canadian province of Ontario, which defines personal information in data protection legislation as follows:
Not all information about individual beneficial owners constitutes personal information. Using Ontario’s public sector privacy legislation as an example, personal information is information that identifies an individual (that is, a natural person) acting in a personal capacity. The context in which the information appears is a factor to be considered in determining whether it is personal information. As a general rule, information about an individual in a business, professional or official capacity is not considered personal information. Ontario’s legislation specifically excludes the name, title, contact information or designation that identifies a person in a business, professional or official capacity from the definition of personal information [emphasis added]. [34]
While the UK modelled its data protection legislation on the EU GDPR, it provides for some domestic exemptions where the EU GDPR does not. The UK’s Data Protection Act 2018 provides the following exemption from specified UK GDPR provisions: “The listed GDPR provisions do not apply to personal data consisting of information that the controller is obliged by an enactment to make available to the public, to the extent that the application of those provisions would prevent the controller from complying with that obligation”. [35] It subsequently states that:
Since the registrar is required by the Companies Act and Economic Crime (Transparency and Enforcement) Act to make information available to the public, they’re entitled to rely on this exemption. Therefore, they have an exemption from some elements of UK GDPR, including: the requirement to provide “privacy notices” to individuals, the requirement to provide personal data in response to subject access requests, the requirement to rectify personal data when it is inaccurate, the requirement to comply with requests to be “forgotten”, most of the principles of UK GDPR. [36]
Implementing agencies should avoid defaulting to a de-risking approach when it comes to privacy, resulting in overly restrictive access models. This, in turn, could affect the overall effectiveness of registers and their ability to achieve their stated aims.
Identifying users and understanding their needs
A key step in designing a BO access regime is to identify relevant user groups and understand their needs, as part of best practice in agile approaches to the development of digital services. Irrespective of whether a government is pursuing a limited or broad set of policy goals, a range of users from different groups will fulfil complementary roles. For example, a government aiming to improve procurement and public oversight of the spending of public funds may consider procuring entities, tax payers, and the general public as potential users of information about companies involved in public procurement. Academic researchers can also inform policy by analysing trends in contracting, or by piloting the development of evidence-based indicators to support risk prevention and detection. [37]
Many jurisdictions implementing BOT specifically to comply with international AML standards only provide access to a limited number of user groups, such as competent authorities and AML-regulated entities. However, even if a jurisdiction is pursuing a limited set of objectives, a broad range of users may still be relevant to those aims. For example, for AML purposes, procuring entities, investigative journalists, and data service providers also play a critical role. Often, these different users work together: law enforcement may receive intelligence from investigative journalists and obliged entities, who may use solutions provided by data service providers to identify risk. Therefore, limiting access to few or narrowly defined user groups is likely to limit the impact of reforms.
Implementing agencies should consider the full range of relevant users and aim to understand the complementarity between different users’ contributions to policy goals. Due to the transnational nature of many BO networks, implementing agencies should consider both domestic and foreign users. No matter which objectives a jurisdiction is pursuing, there will be relevant users from key user groups, including: government users; private sector users; civil society users; and others.
Government users
Government users typically include the following:
- domestic and foreign registrars (e.g. those for other kinds of legal vehicles or assets);
- law enforcement agencies and other agencies which have a legal mandate with respect to the specific policy objectives of the reform (i.e. competent authorities);
- regulators;
- procuring entities;
- other users who are involved in issuing licences or enforcing rules around political party financing, ownership in critical sectors, and asset disclosure by politicians.
Despite this, government users in many contexts face significant barriers to access and use, for example, having to pay to access information or not being able to access information at all due to not being recognised as a competent authority. [38]
Private sector users
Businesses require access to BO information to comply with statutory obligations as part of AML regulations, labour laws, and human rights and anti-corruption legislation. They also require access to BO information in order to conduct due diligence in transactions to help understand and manage risk, including in potential suppliers and supply chains. AML-regulated businesses may have specific requirements to access, use, and report discrepancies with centrally held BO information as part of Know Your Customer (KYC)/Customer Due Diligence (CDD) requirements. [39]
However, a wider range of businesses can benefit from using BO information for purposes such as countering fraud and conducting due diligence, including to ensure they are compliant with sanctions and other regulatory requirements. [40] This could include reviewing information about counterparts in transactions, supply chains, and – for those participating in public procurement – other businesses doing business with the government. It is also important to acknowledge the diversity in the structure, size, and budgets of private actors, as these will have direct bearing on their capacities and their possible use of BO information. [41]
Commercial providers of data solutions and services also play an important role in the BO information ecosystem. These intermediaries address barriers to effective BO data use, including around access, quality, format, and analytical capacity. [42] Given their specific efforts in addressing barriers to data across borders, policy makers in jurisdictions that aim to understand transnational BO networks may want to pay particular attention to potential access to non-domestic commercial providers of data solutions.
Civil society users
Non-governmental organisations (NGOs), CSOs, the media, and academics use BO information to play a critical role in providing oversight and accountability in democratic societies, as well as informing policy. Even in contexts with narrow and specific policy goals, such as AML/CFT, these users have a critical role to play, as many law enforcement agencies actively draw from their experience (see Box 2). International collaboration between third-sector users can provide invaluable support to the work of law enforcement tackling international crime and fraud. [43] Civil society has proven valuable in improving the effectiveness of reforms, including through feedback on usability (see, for example, Box 7).
Other users
Implementing agencies should also consider users outside these groups. For example, where policy goals include guaranteeing transparency and accountability over the allocation of public funds, all taxpayers are potential users of BO information. Anyone may require information about specific businesses they have a relationship or transactions with, such as tenants needing to know who is ultimately behind a company owning their building or apartment, or to ensure they comply with sanctions. [44] Particularly where objectives include attracting investment and fostering economic growth, potential and prospective investors benefit from access to BO information.
Conducting user research
Once relevant users have been identified, research is essential to design, review, and strengthen laws and policies as well as to develop systems that enable users to access the information they need. [45] How users find information, which specific challenges they face, and which data sources they use can vary across contexts. Agencies responsible for BOT reforms can use existing resources as a basis to test and refine their understanding of user needs in their own context.
User research is part of a privacy-sensitive approach, as it allows researchers to identify what information users need access to and for which specific purposes. It enables policy makers to be intentional and ground access rights with evidence about users’ needs rather than on broad assumptions. This should help implementing agencies to not be overly cautious and develop restrictive access models, which could affect the overall effectiveness of registers and their ability to achieve their stated aims.
User research can be carried out at any stage of the implementation cycle, and it can continue to inform iterative improvement. In jurisdictions that already have an access regime in place, it allows gathering feedback on current users’ experience. In places where BO information is not yet available for use – or not by all relevant users – policy makers can seek to understand user experiences with related information sources, including other company information and non-domestic BO information, as well as understanding their broader goals. [46] Implementing agencies can be guided by existing resources to help plan and conduct user research (see Figure 1). [47] A number of jurisdictions have adopted a user-centred approach to maximise the effectiveness of their reforms (see Box 3).
Figure 1. Example of using Open Ownership’s framework for usable beneficial ownership information to understand user needs
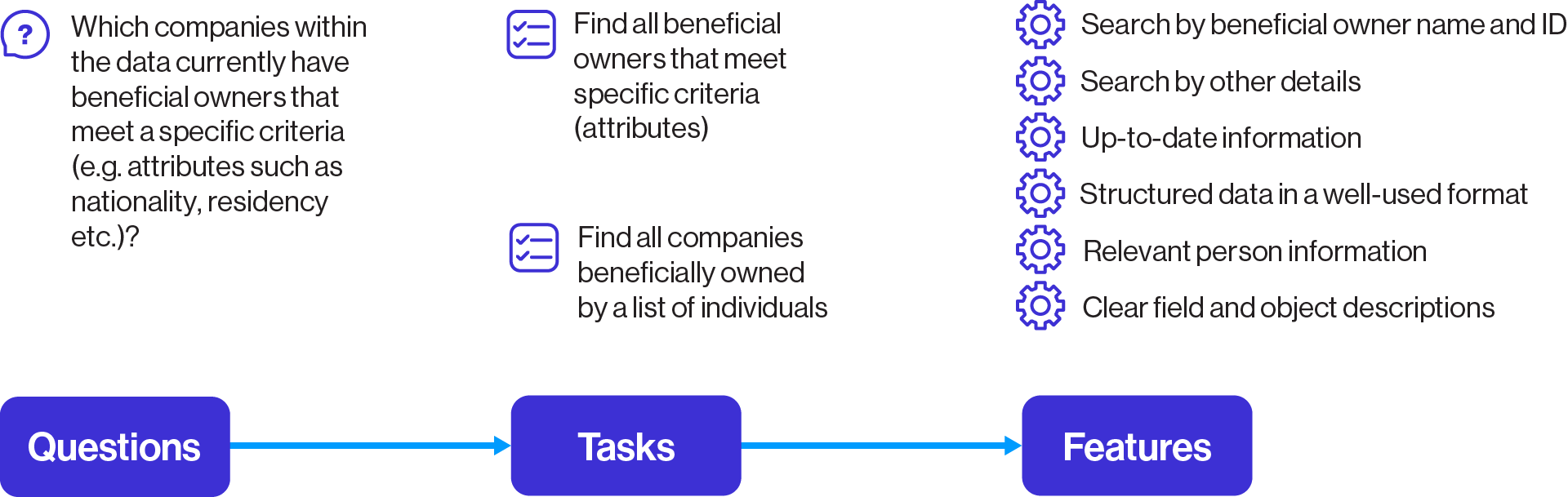
Open Ownership’s framework for usable BO information illustrates how understanding users’ questions can help identify the tasks they need to undertake to answer these questions, which can in turn guide decisions such as what features may be required for BO register’s data to enable these tasks to be completed. Source: Open Ownership, Usable beneficial ownership data.
Box 3. A user-centred approach to developing a beneficial ownership register in the Philippines
In 2024, the Securities Exchange Commission (SEC) of the Philippines (the agency in charge of BOT reforms) conducted user research with selected law enforcement, tax, and competent authorities. The research comprised:
- a feedback form to understand users’ perspectives on the timeliness, accuracy, and adequacy of the SEC’s BO data; and
- interviews with selected agencies to get a more detailed and targeted understanding of their current access to and specific needs in using BO data, as well as potential avenues for improvement.
These aimed to inform the development of the BO register, a review of the SEC’s policy guidance, and an understanding of users’ capacity gaps. Interviews provided concrete considerations based directly on user experiences. For example, some participants flagged the issue of a lack of reliable identifiers for individuals – especially foreign nationals – and historical information. They also mentioned that rather than access on request, direct access would greatly improve the utility and impact of the information on investigations. User experiences and recommendations guided decisions about access provisions and technical requirements of the BO information system and subsequent policy reforms. The research also led to concrete data protection considerations, such as ensuring direct access to BO data included access controls and audit trails.
Research on the SEC’s BO data also showed that the absence of a centralised registry created challenges for data retrieval and verification. This motivated a shift to a centralised digital register with enhanced accessibility in order to improve data usability for both regulators and investigators. [48] In 2025, the SEC issued a Memorandum Circular (MC) increasing the amount of information collected and expanding access to obliged entities, the media, and the general public, subject to privacy considerations. [49] In response to requests for historical data, it also now requires the collection of dates when a person becomes a beneficial owner.
Within and across different groups, data users can have varying needs depending on what they are seeking to achieve, and these can change as initial questions may generate additional, unforeseen questions which create new sets of needs. This suggests that it is impractical to categorise user groups – and access layers – by only one specific way they use data. [50]
For example, in seeking to identify and analyse trends in market concentration, a competition regulator or a business journalist may need to know whether the same person owns multiple businesses, along with changes over time, but will not necessarily need to know the names of any beneficial owners. [51] By contrast, an investigative journalist or an analyst working for a financial intelligence unit establishing connections between legal vehicles, individuals, and assets related to a criminal network will likely be trying to specifically identify an individual. These users will need a lot more identifying information, including names and other identifiers such as nationalities and dates of birth, but for a much smaller number of individuals and companies.
On the other hand, a financial or academic institution dealing with high volumes of transactions or data to analyse may need technical solutions such as application programming interfaces (APIs) to ingest information into their internal KYC/CDD platforms or research software. They may also rely on commercial providers of data solutions and services, who will in turn require APIs and bulk data to ingest BO datasets into the services offered to end users. [52] For all users trying to identify trends and analysing large amounts of data, access on a per-record basis, company by company, will make their work practically impossible.
Research also shows that most data users share common needs:
- direct and timely access to usable, up-to-date, and historical information, including on foreign legal vehicles and individuals;
- the ability to easily retrieve, and flexibly search, and process information; [53]
- the ability to identify whether records about individuals, legal vehicles, and assets appearing in the same or different registers refer to the same or different subjects (this is referred to as entity resolution), and to understand relationships between them; and
- a minimum level of accuracy in order to be able to draw conclusions with confidence.
Designing access layers
Once the objectives of the reforms have been defined, all relevant users have been identified, and their needs have been mapped out, different layers of access can be designed. Layers are typically defined by:
- who has access, and for what purpose, including authenticating permissions if necessary;
- what information users have access to, in which format, and how they access such information – the usability features – ensuring user needs are met; and
- appropriate safeguards, based on the amount of information that can be accessed and audited, and how this information can be used and shared.
Considering more than two layers may allow for a better balance to be struck between access and privacy, and may lead to more effective and impactful access regimes.
Who has access and for what purpose
Layers of access are either publicly accessible or limited to specific users or groups.
Public access
Where possible, providing public access is by far the easiest way to ensure the broadest range of relevant users have access to some BO information. To illustrate, in jurisdictions where access is indiscriminately given to the public – such as in Armenia, Ecuador, Nigeria, and the UK – a range of user groups may access information in the same way as the public. In these contexts, government users are often significant users of publicly available information, as this precludes the need for inter-agency data-sharing agreements and mechanisms. Public access therefore removes many of the frictions associated with other forms of more restricted access.
Research shows that these frictions are an overwhelmingly common feature of many access models, particularly when it comes to transnational investigations. The effectiveness of AML efforts and other policy areas may also be affected by the additional friction created by more complex access systems. There is a risk that where each jurisdiction develops a bespoke access system, a fragmented cross-border system emerges – with different definitions, use cases, application processes, and waiting times. To illustrate, Transparency International has extensively tested and documented the divergence in access methods and uneven access provisions in the EU under different AML Directives. [54] This administrative complexity can make it significantly harder for legitimate users to access and use information at scale or across borders, undermining the very objectives the framework is intended to support.
Certain reform objectives more clearly mandate public access. For example, the Latvian government has argued that everyone needs to be able to access BO information in order to comply with sanctions. [55] Certain countries pursuing objectives of public procurement and natural resource governance that do not provide indiscriminate public access to information on all legal vehicles have opted to provide public access to relevant companies, i.e. those which bid on public contracts or have extractive licences. Following the CJEU ruling, legal arguments based on EU case law are emerging in support of the idea of financial transparency as a constitutional value, with access to BO information for legal vehicles as necessary for the functioning of democracy. [56]
As evidenced with the EU’s experience, public access does not guarantee effective access to usable data. [57] Implementing a layer of public access does not preclude governments from designing additional, dedicated layers for specific user groups that have features that meet a more extensive set of needs. However, a public access layer can ensure that foreign users or users that may not fall neatly into recognised or pre-defined categories – such as leaseholders, independent experts, grassroots activists, and those without formal institutional affiliations – that often play a critical role in identifying wrongdoing, do not struggle to meet eligibility criteria. Other frameworks for access, such as legitimate interest access (LIA), are evolving, and it is not yet clear what the most effective and impactful approaches are. Maintaining an access layer for the general public (e.g. through a basic portal) without needing to demonstrate a legitimate interest may be prudent and desirable.
Layers limited to specific user groups
While research suggests that different types and categories of users have overlapping needs, in practice, access is often organised around categories of users and purpose. Multiple categories of users can have access to the same layer with the same features, with different ways of authenticating permissions. While demonstrating the permission to access information in cases where the information is not openly available typically remains centred on who will access, layers can be organised around the minimum information and flexibility of use necessary. User groups accessing the information for a specific purpose may, for example, be defined as users with a legitimate interest (see Box 4).
Authenticating permissions
When an access layer is restricted to certain users, requirements can be put in place for authentication of permissions. This can involve demonstrating being a specific individual user or part of a category of users. For government users, this may involve being restricted to access the information in controlled work environments. For AML-regulated entities, this may involve validating a registration number with a regulator, and receiving API credentials. It can also involve authenticating parties deemed to have a legitimate interest in accessing the information (see Box 4).
To operationalise this, application procedures need to be put in place. These should not be overly burdensome. Many jurisdictions rely on sworn statements or supporting evidence. Identity verification processes can provide assurances on who specifically is accessing the information and further support accountability. Regulated entities or government agencies may designate specific staff members to access information. Users may need to be required to log in and use issued access codes.
Jurisdictions should avoid putting in place systems where applicants may be subject to more scrutiny than the beneficial owners themselves, and creating situations where critical users like journalists and researchers face greater privacy intrusions than the individuals whose interests are subject to disclosure.
Box 4. Features of effective access on the basis of demonstrating a legitimate interest
An increasing number of jurisdictions are implementing BO registers with access based on legitimate interest. These include EU Member States, UK OTs, and UK Crown Dependencies. Other jurisdictions, such as Zambia, are also considering expanding access on the basis of legitimate interest. These jurisdictions provide examples from which features of effective LIA regimes can be identified. Further legal developments in the EU suggest more personal data related to companies and other legal vehicles may be subject to the demonstration of legitimate interest in future, further highlighting the need to develop effective LIA systems. [58] Access on the basis of legitimate interest was challenged in Austria in 2025, where the Constitutional Court granted that access to the BO register to anybody with a legitimate interest does not violate the beneficial owner’s right to data protection. [59] Beyond the features outlined below, all of the other aspects of effective access discussed in this briefing also apply to LIA.
Implementing governments should consider whether they can align LIA frameworks with other relevant jurisdictions and agree on mutual recognition, as in AMLD6. This means that LIA in one jurisdiction is valid in another. Aligning LIA frameworks across jurisdictions has the potential to reduce the administrative burden on both applicants and registrars.
Defining legitimate interest and user groups
Legitimate interest should be holistically defined in line with policy goals, covering all parties that are able to use the information to achieve the stated objective. Where legitimate interest is defined in narrow terms in relation to AML, it should be defined not just with respect to the crimes of money laundering, but also all underlying and predicate crimes.
LIA frameworks should cover all relevant users. For example, frameworks should not discriminate between whether prospective users are domestic or foreign, particularly where these both have a role to play in achieving policy objectives. Relevant groups should be predefined as having a legitimate interest by default, as this will both ease the burden of administering access requests and minimise the risk of excluding users. Groups should be defined to include all individuals who are a member of a profession (e.g. journalists), industry (e.g. media), or conducting activity (e.g. expressing oneself in the media).
To illustrate, legitimate interest should be defined around an individual being engaged in journalistic activity rather than be limited to registered journalists. For example, the EU AMLD6 and France have predetermined that certain groups of users – based on their professions and activities – have a legitimate interest (e.g. “persons acting for the purpose of journalism, reporting or any other form of expression in the media”). [60] There is no distinction between whether these users are domestic or foreign.
In addition to specific user groups, any other individual should be able to demonstrate a legitimate interest on a case-by-case basis, even if they do not belong to any of the predefined user groups. This is so that the impact of a BO register is not limited due to any user groups having been inadvertently left out. The list of user groups predefined as having a legitimate interest should be reviewed and updated on a regular basis.
Access process
The process by which to demonstrate legitimate interest should not be unduly burdensome. Following from the above, any prospective user should only need to prove they are part of the user group defined as having a legitimate interest, rather than needing to demonstrate working on a specific case. In some cases, it will be justified to provide access to an organisation (e.g. an NGO or a service provider) rather than an individual, and application processes should accommodate this.
Requirements for prospective users to provide supporting evidence should be realistic, flexible, and not unduly burdensome. For example, a track record in publishing articles related to money laundering or a press pass may qualify as evidence of legitimate interest in AML, but not all individuals engaged in journalistic activities with a legitimate interest will be able to produce this type of evidence. Supporting evidence requirements should be flexible. Where supporting documents are required, there should be clear guidance and objective criteria on what constitutes supporting evidence for each user group, and when an evidence threshold is met.
For example, in order to access BO information in Ireland, an individual would have to indicate how a specific legal entity about which they are seeking information “is connected with persons convicted (whether in Ireland or elsewhere) of an offence consisting of money laundering or terrorist financing, or holds assets in a high-risk third country”. [61] Possibly as a result of this high threshold, there was no use of BO information on the Irish register through LIA in the first four months of 2024.
To reduce the administrative burden on both applicants and registrars, implementers should not overly rely on supporting evidence and instead consider whether a sworn statement, in combination with robust identity verification – as well as strict liability offences for any misuse of BO data as a result of the access – would suffice. To illustrate, while France’s LIA process includes the requirement for NGOs to submit examples of work on AML, the Danish process simply requires the submission of a sworn statement, including an indication of which defined LIA category a user falls in. [62]
Governments should explore whether decentralising decision-making around legitimate interest applications, in whole or in part, is feasible. For example, in Luxembourg, the press agency was able to issue digital tokens to journalists to access the BO register, reducing the administrative burden on BO registrars. There is a potential role for an independent body to be responsible for and oversee the access process, although this has not been implemented in any jurisdiction at the time of writing.
Due to the time sensitive nature of certain use cases of BO information – e.g. criminal investigations – a short and defined statutory period for processing applications should be set (e.g. one week). For example, the EU’s AMLD6 defines 12 working days as a processing period, while the UK’s Trust Registration Service LIA framework for trusts gives a general timeframe of approximately eight weeks, severely limiting the timeliness of financial crime investigations.
Application processes should include an appeal and review process for situations where applicants believe a decision has been made in error. This does not need to extend to all rejections (e.g. when on the basis of an incomplete application), but should include all cases where discretion has been applied.
When access is granted, this should be valid for a set period of time (e.g. one year) during which legitimate interest does not need to be demonstrated. Those with access should be required to rescind their access when they believe they no longer possess a legitimate interest (e.g. change of job). Authorities may also require renewal if they suspect legitimate interest to have lapsed. There should be clear evidence for this suspicion so these powers are not used arbitrarily.
In all cases, the access process should be clear for potential applicants, and details should be publicly available with relevant documents and accompanying guidance. For example, both France and Denmark have a dedicated webpage to its LIA framework, including details on the legal basis, the process, the application form, terms of use, and guidance on supporting evidence. [63] By contrast, in Ireland there is little information on the access process, and the application form is only available upon request by email. [64]
Cross-border data use
Across different user groups, accessing foreign registers is often described as one of the key barriers to effective data use. [65] As many use cases require understanding transnational BO networks, implementing agencies should also consider enabling cross-border data use. This can involve enabling access to foreign users, either through public access or through dedicated mechanisms, or enabling access to transnational portals or search engines.
Many access mechanisms have technical and operational gaps that need addressing to enable effective use (see Box 5). Even when users can access data from multiple jurisdictions, a lack of reliable identifiers means entity resolution can still be challenging. Commercial data providers and some NGOs have been trying to fill this gap by cleaning, structuring, and aggregating data from different places, and developing tools to enhance data analytics options. [66] However, commercial solutions can be costly and inaccessible to some data users. In the absence of mechanisms that allow for this, many users across different user groups value publicly accessible registers. [67]
In terms of data protection, cross-border access can constitute a data transfer. Data protection often has specific requirements for the transfer of personal data outside of its jurisdiction. It may be necessary to consider whether other jurisdictions have domestic legal systems that offer individuals sufficient protection of personal data, and have adopted adequate safeguards for access.
Box 5. Access mechanisms for beneficial ownership information from multiple jurisdictions
There are a range of different mechanisms to access or share BO information across borders. These mechanisms vary in the number of participating jurisdictions, the purposes for which information can be used, and who can access the information. For example, initiatives such as the GlobE Network, the Egmont Group, the Asset Recovery Inter-Agency Networks (ARIN), and INTERPOL facilitate access to information and provide channels for collaboration and intelligence-sharing between law enforcement, judicial, and investigative authorities of a large number of participating countries.
Many mechanisms rely on the submission and processing of a request, meaning that the time it takes to access information can vary. Needing to request information from multiple jurisdictions can lead to critical delays, and the timeliness of access to foreign information has been a persistent challenge for authorities. [68] The bilateral “Exchange of Notes” mechanism between law enforcement of the UK and the OTs requires responses to requests within 24 hours. However, it only covers a small number of participating jurisdictions. [69]
In contrast, the Automatic Exchange of Information (AEOI) for tax purposes covers the majority of jurisdictions. Under this mechanism, information about the beneficial owners of companies holding financial assets that are tax resident in participating jurisdictions – collected by financial institutions under AML obligations – is shared by those financial institutions with tax authorities, and exchanged with respective jurisdictions at the end of each tax year. The information is sent in bulk in a highly structured format according to a common standard. However, this data is received once a year at different times from different jurisdictions, and only among the tax authorities of some countries.
Many mechanisms were developed for a specific policy objective and involve one type of government agency. Some initiatives, such as the European Joint Investigation Teams (JIT) were designed with collaboration at their core; they facilitate direct exchange of information and cooperation between prosecutors, law enforcement authorities, and judges in real time and organise joint operations across borders. [70] Yet, these are broader than just BO information and usually have a very specific mandate.
Regional and domestic efforts to enable direct access to usable information to a wide range of users are promising, but have not yet been implemented. For example, the access regime in the EU’s 2024 AML package should allow a range of government and non-government users from any jurisdiction to access information from all EU registers, once they have demonstrated their legitimate interest. [71] This information should also be accessible through a single platform, the Beneficial Ownership Registers Interconnection System (BORIS), which enables searching across multiple registers. [72]
Usability features for each layer
Each access layer is defined by which information is accessible through it, in which format, and how flexibly it can be used. Taken together, these are features of usable BO information. Drawing on Open Ownership’s framework for usable BO data, the main types of features to be considered are those related to scope, content, delivery, and search (see Box 6). [73]
Box 6. Features of usable beneficial ownership data
Open Ownership has developed a framework for producing and assessing usable data, comprising a set of data features that are key to usability. [74] At the time of writing, this live framework is being tested in various contexts to review and assess registers’ usability from the perspectives of those using the data. This can provide guidance to consider which features should be accessible to users under a jurisdiction’s access regime.
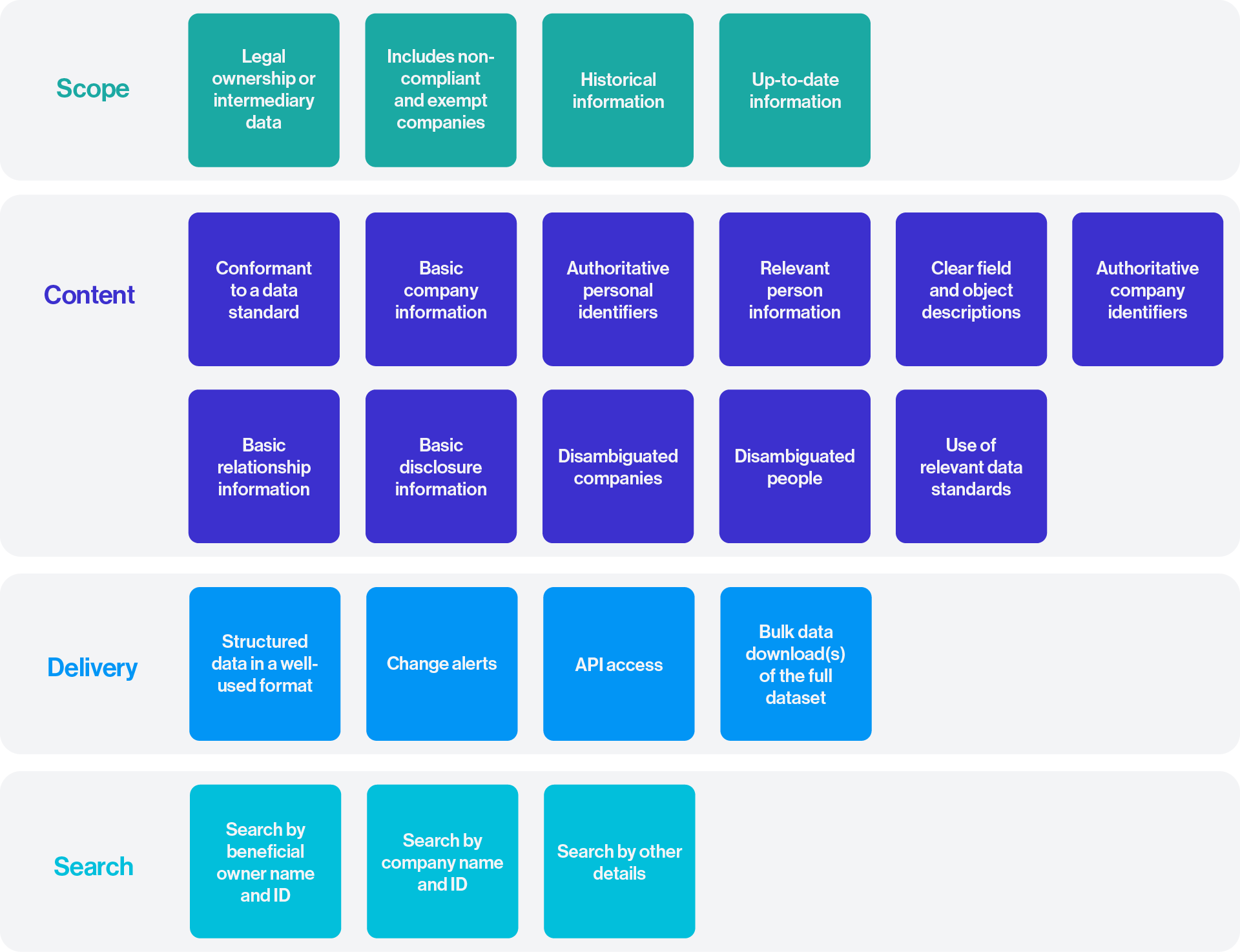
Source: Open Ownership, Usable beneficial ownership data.
Scope
Usability features relating to scope cover considerations including which legal vehicles are included (e.g. all domestic legal entities, or just those involved in contracting with the government), and whether historical information and details about intermediaries in a company’s structure should be included.
In order to close loopholes, jurisdictions should consider access to BO information for all legal vehicles – including trusts and other legal arrangements – subject to BO disclosure requirements. There are differences between entities and arrangements as legal vehicles, and historical differences in their use, and the transparency requirements they have been subject to. However, arguments for transparency around companies increasingly apply to trusts, and vice versa. As illustrated by a 2023 UK consultation about access to BO information: “Trusts can also derive benefits from the state and, indeed, companies can also be primarily family affairs, yet family companies are exposed to the same transparency requirements as other companies”. [75]
Content
Content features consider questions such as: What type of information do users need to answer their questions? Which data fields can a user access? Does this include sensitive information? Which identifiers are used and accessible? Content features, including the use of reliable identifiers, are crucial to meeting universal user needs, such as the ability to identify and distinguish between beneficial owners and companies. [76]
International standards may have a bearing on which data fields certain users should be able to access. For example, the FATF’s Recommendation 24 requires competent authorities to have access to sufficient information in order to be able to identify individuals. [77] Data features go beyond which information fields from declarations are made available. For example, research has shown that information about the data – such as whether or not a register holds information about a particular legal vehicle or individual – or pseudonymised information is also valuable to users. [78] As these do not contain personal information, it may be possible to make this available to a larger group of users with fewer safeguards.
Limiting access to sensitive and protected information
Registers should limit the access for certain layers of users to certain sensitive or protected information, for example, where someone is demonstrably exposed to disproportionate risks (see Protection regimes). For instance, while a competent authority may have access to ID numbers, it is sensible to limit access to ID numbers for non-government users. In addition to data minimisation, it may be necessary to limit access to certain fields to minimise specific risks. An example of this is dates of birth. Dates of birth are almost always provided as an additional identifier which helps with entity resolution. However, privacy impact assessments in the UK deemed a full date of birth to pose a serious risk to identity theft. By providing only the month and year of birth, this would still be a useful additional identifier for identity resolution while decreasing the risk of identity theft. [79]
Delivery and search
Delivery features cover whether the information is searchable through a portal, accessible through an API or in bulk (see for example, Box 7), and in which format. Adopting widely used data formats (e.g. ISO 3166 for country codes, ISO 8601 for dates), structures (e.g. JSON, CSV, XML, etc.), and identifiers (e.g. legal entity identifier) can significantly support users in interpreting data from different countries. [80] Search features include whether users can search by legal vehicle, by natural person, or both, and whether they are able to search by name, ID, or other criteria.
Both categories of features have a bearing on privacy infringement. Some implementers have taken the approach of limiting searchability to companies for certain access layers. While this may satisfy some use cases, it will limit usability for many others, including investigations.
Box 7. How delivery features affect usability in practice
Transparency International France and the Anti-Corruption Data Collective attempted to analyse patterns and risks related to real estate ownership in France. In their report, they highlight how their lack of access to data in bulk required them to manually go through five million web pages, significantly adding to the cost of doing the analysis. [81] They encouraged the French government to provide access to BO information through APIs to improve data use effectiveness. [82]
In Norway, following the 2024 launch of the BO register, Tax Justice Norway and Open Ownership set out to assess the extent to which information contained in the register is accessible and usable. Findings highlighted strong usability features, as information was available as structured data with authoritative company identifiers and in standardised formats. These features enabled the data to be integrated and analysed with other registers, such as the country’s company register and PEP datasets.
A stable and functioning API enabled the systems to easily interact with others. However, while it was possible to retrieve data through an API, there was no public portal through which to find information, meaning a level of technical proficiency was required to access the data. Users who had the ability to do so also faced limitations. For example, the API only allowed one query within a set time period, and did not allow searching by company or beneficial owner name, only by company number (which users could obtain from separate registers). Taken together, these constraints limited the ability to conduct systemic, large-scale analysis, thereby limiting the register’s effectiveness. [83]
In the UK’s LIA system for information on trusts, applicants submit information about a trust to receive information about that trust’s beneficial owners. This effectively means users are only able to search by trust – and not by beneficial owner – and receive the information on a per-record basis rather than in bulk, limiting usability.
Safeguards
To support the responsible use of data and prevent its misuse – including by government users – implementing agencies should consider the degree of interference on privacy posed by each layer, and put in place appropriate safeguards. The interference depends on the amount of information and flexibility of use provided, as well as the number of people who will access the information.
Safeguards can minimise risks, help enforce purpose limitation, and offer a means of recourse in the case of misuse. Safeguards are not mutually exclusive. They can be complementary and can include:
- access logs and audit trails;
- terms of use; and
- protection regimes.
Access logs and audit trails
Implementing governments should consider putting in place access logs and audit trails for layers of access that are not open – particularly for access to large amounts of sensitive data, including for government users. This helps ensure purpose limitation and accountability in cases of misuse. Data users interviewed in the Philippines recommend establishing control and audit trails to show who accessed the data, when, and for what purpose. [84]
Access logs and audit trails can assist with accountability for data use. Operationalising this requires user authentication and tracking how they each use the information. While audit trails can be used for public access (e.g. IP tracking) it is more often associated with layers limited to specific users.
Under no circumstance should information on who has accessed BO information be shared with the companies or beneficial owners in question. For example, AMLD6 and Luxembourg access provisions both explicitly prohibit the sharing of the identities of data users with the beneficial owners or the legal vehicles whose information was consulted. This can jeopardise investigations by tipping off subjects. It can also infringe the privacy of the data users, and may lead to risks of personal harm. [85] To strike a balance, the AMLD6 allows for only the function or profession of the data user to be disclosed to the beneficial owner. For foreign competent authorities, they can apply for information about their access not to be disclosed to the beneficial owner for an initial maximum period of five years. [86] In the British Virgin Islands, companies are automatically notified of the name of the legal person requesting their BO information, and not of individuals. [87] In certain cases, this could still create a tip-off risk or jeopardise individuals.
Access logs should have defined retention periods that are compatible with the purpose of the measures implemented and not be excessive. Unlimited retention of this data could increase the risk of negligent disclosure, and it can cause risks to certain data users, especially investigative journalists and NGOs.
Terms of use
There should be clear terms of use to provide both clarity to users and for purpose limitation. For example, the French terms of use for users with access on the basis of LIA states: “for users acting for the purpose of journalism, reporting, or any other form of media; NGO representatives and researchers: communicate information to third party only as part of activities justifying their legitimate interest in accessing the latter”. [88] For a journalist investigating money laundering, this does not provide clarity on how exactly the information can be used, including in the context of international cooperation to tackle transnational financial crime, potentially limiting the impact of that journalist exposing wrongdoing. By contrast, the Danish guidance states clearly:
[T]here will be legitimate processing of the information when the press uses information about beneficial owners in their journalistic work, etc., and links specific names of people with their beneficial ownership in articles, etc. Furthermore, third-party data providers have the right to disclose information about beneficial owners as long as they only disclose the information to clients who are either a competent authority, obligated entity or the press in connection with a concluded contract. [89]
While terms of use cannot guarantee purpose limitation, requiring the agreement with terms of use and penalties for noncompliance may deter misuse and provide a basis for recourse.
Particular attention should be paid to the terms of use for where information is made available to third parties, such as commercial data providers. These users should be required to guarantee the quality of the data over time through, for example, the use of data access and acquisition channels directly in the BO register, minimising the risk of alteration or loss during transmission.
Protection regimes
Implementers should provide for exemptions in circumstances where someone is exposed to disproportionate risks. This is a common feature of many BOT regimes and an essential part of responsible implementation. This should focus on mitigating risks emerging from the publication of the data – i.e. knowing that someone is the beneficial owner of a specific legal entity. For instance, a person might be a member of a particular religious community and be the beneficial owner of a company whose activities conflict with the principles of that religion. The protection regime should also include risks emerging from the publication of any of the personal data. For instance, someone who has been stalked and harassed has a legitimate case not to have the combination of their name and address published. A protection regime should have an application system with the possibility to apply to have certain or all data fields protected before these are published, when substantiated by evidence. These should be reviewed according to a set of narrowly defined conditions to avoid creating significant loopholes and abuse. Protected information should be available to certain users, such as to law enforcement agencies.
A 2021 opinion of the EU Advocate General emphasises that protection regimes are not just good practice but a requirement, stating that governments are “obliged to provide for and to grant such exemptions where, in exceptional circumstances, that access would expose the beneficial owner to a disproportionate risk of interference”. [90] Following the CJEU judgement, the UK defended the public nature of its access regime, stating that while it had no “proper purpose filter”, as that was deemed to risk undermining transparency, its access regime was compliant with the European Convention on Human Rights (ECHR) due to the expansion of its protection regime. [91]
Box 8. Examples of access regimes with different layers
The jurisdictions below have access regimes that feature identifiable layers, illustrating what this looks like in practice. They have not necessarily defined their access regimes as layered.
Kenya’s access regime to the Business Registration Service’s (BRS) BO information has three layers. The first layer is access for competent authorities, through: written requests, mostly in the context of information needed for court cases or for quasi judicial proceedings; through a portal, where designated authorised officials are granted access to BO information via a user account provided by BRS; or through an API. [92] If agencies make any change to the list of designated officials, they should notify BRS to request changes in access rights. The second layer is access for AML supervisory and regulatory authorities as well as designated non-financial businesses and professionals who can access information, but not through an API or a user account. Instead, they can download information. Despite access being initially restricted, as a result of the 2018 Executive Order (which has since been anchored in law), BO information regarding companies that have been awarded government contracts is available to the public through the Public Procurement Regulatory Authority’s Public Procurement Information Portal as well. [93] As of 2025, obliged entities such as banks and lawyers also have dedicated access. Banks have the capacity to conduct either individual or bulk searches for a fee, and lawyers can also, once white-listed, conduct searches on the BO information for a fee.
The Philippines primarily collects BO information to make it accessible for competent authorities and law enforcement. However, it also allows controlled information-sharing with a number of government agencies which have signed data-sharing agreements with the SEC with an aim to balance access to BO information with national data protection rules. It also allows public access to subsets of the information for two distinct policy goals. The first is natural resource governance, where the public is now able to access BO data for large-scale metallic mining companies due to the recent enactment of the Fiscal Regime Act. [94] The second is public procurement. Under the 2023 New Government Procurement Act, the Philippines is putting in place a public subset of the register with the Procurement Service of the Department of Budget and Management, the agency which also oversees the Philippines’ government e-procurement system (PhilGEPS). [95] Finally, while seeking to improve data usability through the launch of its digital register HARBOR, the SEC also developed a new rule in 2025, which expands the Commission’s right to grant access to the general public, to the extent allowed by law. [96]
In the EU, Articles 11–15 of AMLD6 outline different layers and processes for accessing BO information. It does not distinguish between access to legal entities and arrangements such as trusts. It also provides for unified access to the Member States’ 27 registers through the system of interconnection of central registers (BORIS), adding that the “interconnection has proven to be essential for an effective cross-border access to the beneficial ownership information by competent authorities, obliged entities and persons with a legitimate interest”. [97]
Article 11 provides for immediate, unfiltered, direct and free access to the information held in the interconnected central registers for competent authorities, without alerting the legal entity or legal arrangement concerned, defining eight categories of national government and EU agencies. It also provides for timely access for obliged entities. The Article defines a subset of information that is available for persons with a legitimate interest, including historical data and a description of the control or ownership structure. It defines 10 categories of users with a legitimate interest, including journalists, NGOs, academics, businesses entering into a transaction with another business, non-EU competent authorities, procuring authorities, and providers of AML/CFT products. It also provides for any additional category of persons who have been found to have a legitimate interest. While certain users such as journalists and NGOs will be able to access the whole register, non-EU competent authorities are only able to access information regarding specific legal entities or arrangements.
Article 13 provides for the access procedure, specifying that users need to provide evidence to enable the verification of the presence of a legitimate interest, the verification of their identity, and clarifying that certain user categories need to specify the relationship to the legal entity or arrangement, and others do not. It provides for access for 12 months, and for mutual recognition in Member States.
Figure 2. Illustrative example of a layered access regime, demonstrating a range of users and purposes per layer, with appropriate data features and safeguards
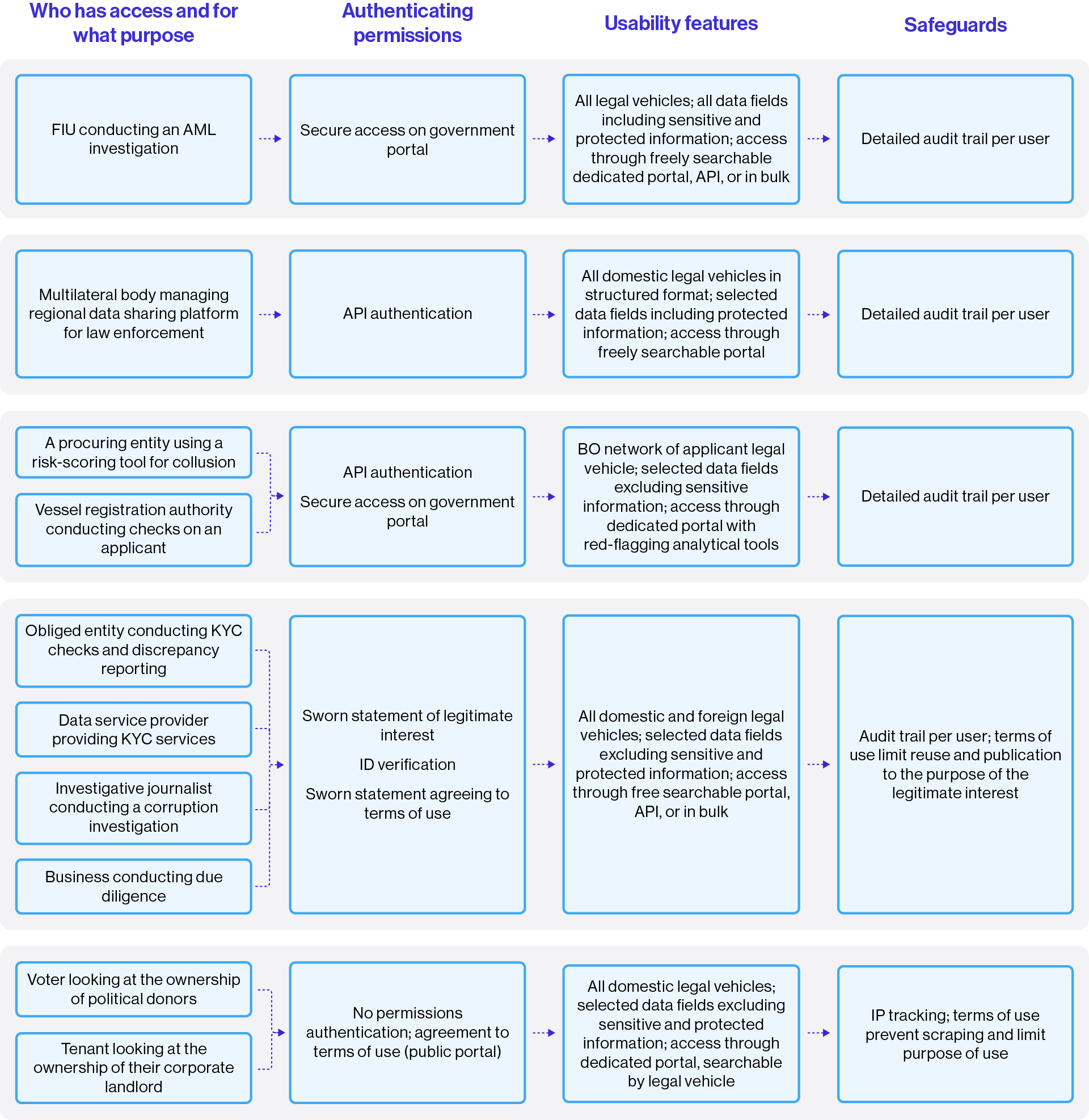
This diagram is an example of a layered access approach. Each layer is represented by a grey box, with a non-exhaustive list of examples of who has access and for what purpose. Additionally, each layer is characterised by permissions authentication (except for the public access layer), usability features, and safeguards. Multiple user groups have access to the same layer. There are dedicated layers for different government users and cross-border access. There is both a public access layer and a layer with access on the basis of legitimate interest, with more extensive usability features.
Additional considerations
In addition to designing access layers, implementing agencies should consider:
- charging access fees;
- monitoring, evaluation, and impact measurement; and
- documenting and reflecting the balance in legal frameworks and systems.
Access fees
To fund reforms, some countries have adopted a business model that includes charging companies and data users a fee to access BO information. Where these fees exist, all user groups have reported that the cost creates barriers to effective use of this information, which is likely to undermine impact. Specific reports came from civil society, government users, and small businesses and financial institutions who explained how, for example, obligations to use a corporate payment card to pay for BO information sometimes meant they were unable to access it. [98]
On the other hand, some governments have adopted an approach where specific data products or data-processing options are only accessible through a fee for certain profiles of users, such as commercial users. For example, the UK’s Companies House charges companies such as credit agencies for some bulk data products, while maintaining free access to publicly accessible data. [99] To complement this, it has also covered rising costs with increasing company incorporation fees. [100] Access fees should not be introduced to mitigate interference with privacy.
Monitoring, evaluation, and impact measurement
Monitoring use through user feedback, consultation, and research can be a helpful way to test whether an access regime is enabling effective access to and use of BO information. Collecting statistics about access across different user groups helps monitor and evaluate how a system is being used, and can form the basis for iterative improvement. This also helps to demonstrate the effectiveness of BO systems, for instance, as part of mutual evaluations of compliance with the FATF Recommendations.
Considering impact measurement – and the role of access and use within this – early in the BOT policy cycle is essential to understanding how policy, legal, and technical provisions support effective access to and use of BO information. Documenting impact is also critical for defending an access regime against legal challenges. The more evidence of access by particular groups and causal links to impact, the easier it is to defend the necessity of the measures.
Documenting and reflecting the balance in legal frameworks and systems
Following the design of an access regime, key features should be anchored in legal frameworks to create a legal basis for access and effective systems. In certain contexts, specific legislation may be required to enable systems development. In these instances, the legislation should enable the design of the system, rather than designing the system itself. [101] Multi-disciplinary teams help ensure that user insights are translated into policy, legal, and systems provisions.
It is also good practice to document the balancing process that has taken place, not only for the purpose of accountability but also to make the system more resilient to legal challenges.
Implementers should adopt an agile approach to systems development, continuing to engage and test services with users through an iterative process. Implementers should follow best practices in data security with respect to the access and sharing of BO information.
Footnotes
[23] Government of Canada, Innovation, Science and Economic Development Canada, “Minister Champagne announces federal corporations need to begin filing their beneficial ownership information”, 22 January 2024, https://www.canada.ca/en/innovation-science-economic-development/news/2024/01/minister-champagne-announces-federal-corporations-need-to-begin-filing-their-beneficial-ownership-information.html.
[24] St Helena Government, “Introduction of a Publically Accessible Register of Beneficial Ownership for St Helena’s Company Registry”, 14 November 2024, https://www.sainthelena.gov.sh/introduction-of-a-publically-accessible-register-of-beneficial-ownership-for-st-helenas-company-registry/.
[25] See: Favour Ime and Tymon Kiepe, Guide to drafting effective legislation for beneficial ownership transparency (Open Ownership, 2024), 12–13, https://www.openownership.org/en/publications/guide-to-drafting-effective-legislation-for-beneficial-ownership-transparency/.
[26] Government of Kenya, “Executive Order No. 2 of 2018 - Procurement of Public Goods, Works and Services by Public Entities”, 28 June 2018, https://s3-eu-west-1.amazonaws.com/s3.sourceafrica.net/documents/118382/Executive-Order-No-2-of-2018-Procurement-of.pdf/.
[27] FATF, The FATF Recommendations: International Standards on Combating Money Laundering and the Financing of Terrorism & Proliferation (FATF, updated 2025), 99,https://www.fatf-gafi.org/content/dam/fatf-gafi/recommendations/FATF%20Recommendations%202012.pdf.coredownload.inline.pdf.
[28] UNODC, “Resolution 10/6 of the Conference of the States Parties to the United Nations Convention against Corruption – Enhancing the use of beneficial ownership information to strengthen asset recovery”, CAC/COSP/2023/L.10/Rev.1, 15 December 2023, https://www.unodc.org/documents/treaties/UNCAC/COSP/session10/resolutions/L-documents/2325375E_L.10_Rev.1.pdf.
[29] OECD (Organisation for Economic Co-operation and Development), Handbook for Second Round Peer Reviews and New Monitoring Processes on Transparency and Exchange of Information on Request (OECD, 2025), https://www.oecd.org/content/dam/oecd/en/networks/global-forum-tax-transparency/handbook-for-second-round-peer-reviews-and-new-monitoring-processes-on-transparency-and-exchange-of-information-on-request.
[30] EITI, EITI Standard 2023, (EITI, 2023), 19–20, https://eiti.org/sites/default/files/2024-04/2023%20EITI%20Standard_Parts1-2-3.pdf?hash=1770634800.
[31] Official Journal of the European Union, “Directive (EU) 2024/1640 of the European Parliament and of the Council”, 31 May 2024, https://eur-lex.europa.eu/legal-content/EN/TXT/HTML/?uri=OJ:L_202401640&qid=1718774932504.
[32] See, for example, the privacy impact assessment conducted by the UK: UK government, Transparency and Trust: Enhancing the Transparency of UK Company Ownership and Increasing Trust in UK Business – Privacy Impact Assessments (Department for Business Innovation & Skills, 2014), https://assets.publishing.service.gov.uk/media/5a7ea73be5274a2e87db10cb/bis-14-884-transparency-and-trust-company-ownership-privacy-impact-assessments.pdf.
[33] GDPR, Article 4 (1).
[34] Brian Beamish Commissioner, Information and Privacy Commissionary of Ontario, Office of the Information and Privacy Commissioner of Ontario Submission on Consultation Paper: Strengthening Corporate Beneficial Ownership Transparency in Canada (Brian Beamish Commissioner, 2020), https://www.ipc.on.ca/en/media/3288/download.
[35] Data Protection Act 2018, Schedule 2, Part 1, Paragraph 5.
[36] Companies House, “Personal information charter”, n.d., https://www.gov.uk/government/organisations/companies-house/about/personal-information-charter.
[37] Tello Arista et al., Using beneficial ownership data for large-scale risk assessment in public procurement.
[38] Julie Rialet, Understanding beneficial ownership data use (Open Ownership, 2025), https://www.openownership.org/en/publications/understanding-beneficial-ownership-data-use/.
[39] See: European Banking Authority (EBA), Consultation Paper: Proposed Regulatory Technical Standards in the context of the: EBA’s response to the European Commission’s Call for advice on new AMLA mandates (EBA, 2025), https://www.eba.europa.eu/sites/default/files/2025-03/9bc83e61-e9a1-4e91-93de-2af8325e0182/Consultation%20Paper%20on%20Response%20to%20Call%20for%20Advice%20new%20AMLA%20mandates.pdf.
[40] Sadaf Lakhani, The use of beneficial ownership data by private entities (Open Ownership, 2022), https://www.openownership.org/en/publications/the-use-of-beneficial-ownership-data-by-private-entities/.
[41] Michael Barron and Tim Law, Beneficial Ownership Transparency Exploring the Private Sector Use Case, (Center for International Private Enterprise, 2023), https://www.cipe.org/wp-content/uploads/2023/08/Beneficial-Ownership-Transparency_CIPE_ACGC_2023.pdf; Lakhani, The use of beneficial ownership data by private entities; Julie Rialet and Mark Hays, What’s in it for business? The US case: Lessons from private sector and civil society advocacy for beneficial ownership transparency reforms (Open Ownership, 2023), https://www.openownership.org/en/publications/whats-in-it-for-business-the-us-case/.
[42] Rialet, Understanding beneficial ownership data use, 14–15.
[43] For example: OCCRP, “Beneficial Ownership Data is Critical in the Fight Against Corruption”, 30 November 2022, https://www.occrp.org/en/project/beneficial-ownership-data-is-critical-in-the-fight-against-corruption; Tracie Mauriello, “Explore the latest tool to power up investigations via the Offshore Leaks database”, International Consortium of Investigative Journalists, 14 January 2025, https://www.icij.org/inside-icij/2025/01/explore-the-latest-tool-to-power-up-investigations-via-the-offshore-leaks-database/.
[44] Adam Travis, “The Organization of Neglect: Limited Liability Companies and Housing Disinvestment”, American Sociological Review 84, no. 1 (2019): 142–170, https://doi.org/10.1177/0003122418821339; Rachel Holliday Smith, “More Money? Pushy Landlord? Your Emergency Rental Assistance Program (ERAP) Questions Answered”, The City, 7 March 2022, https://www.thecity.nyc/2022/03/07/new-york-city-landlord-emergency-rental-assistance-program-erap-questions-answered/; Ministry of Justice of the Republic of Latvia, “Latvijā arī turpmāk informācija par patiesajiem labuma guvējiem būs publiski pieejama”, 6 April 2023, https://www.tm.gov.lv/lv/jaunums/latvija-ari-turpmak-informacija-par-patiesajiem-labuma-guvejiem-bus-publiski-pieejama.
[45] See, for example: Rialet, Understanding beneficial ownership data use and Open Ownership, Usable beneficial ownership data. Building on interviews with nearly forty data users from all user groups across different countries, these resources outline most common user needs and how technical features of BO registers’ data help meet them.
[46] Rialet, Understanding beneficial ownership data use, 25.
[47] Open Ownership’s guide to doing user research for BO systems provides practical guidance to support implementers of BOT reforms with methodologies to better understand their users. See: Open Ownership, A guide to doing user research for beneficial ownership systems (Open Ownership, 2024), https://www.openownership.org/en/publications/a-guide-to-doing-user-research-for-beneficial-ownership-systems/.
[48] Maricel Baltazar and Emily Manuel, Beneficial Ownership Data Use Research Report (Unpublished, 2024).
[49] Philippines Securities and Exchange Commission, “SEC MC No. 15, series of 2025 – Revised Beneficial Ownership Disclosure Rules”, 22 December 2025, https://www.sec.gov.ph/mc-2025/sec-mc-no-15-series-of-2025.
[50] Rialet, Understanding beneficial ownership data use, 22.
[51] Rialet and Hays, What’s in it for business?
[52] Rialet, Understanding beneficial ownership data use, 14–15.
[53] Here, “processing” refers to taking any action on data. See: Information Commissioner’s Office, “Processing” in “Data protection principles, definitions, and key terms”, n.d., https://ico.org.uk/for-organisations/advice-for-small-organisations/getting-started-with-gdpr/data-protection-principles-definitions-and-key-terms/#processing.
[54] Transparency International, “Countdown to new EU beneficial ownership rules: Testing progress on legitimate interest access”, 30 September 2025, https://www.transparency.org/en/news/countdown-to-new-eu-beneficial-ownership-rules.
[55] Ministry of Justice of the Republic of Latvia, “Latvijā arī turpmāk informācija par patiesajiem labuma guvējiem būs publiski pieejama”.
[56] Jan Oleksiuk, Polish Academy of Sciences and Gniewomir Wycichowski-Kuchta, “Financial Transparency as a Constitutional Value in the EU and ECHR System: The case of Beneficial Ownership Transparency” (Presentation, Open Ownership, World Bank, and the University of Sussex, Brighton, 26 February 2026).
[57] Tymon Kiepe, “Striking a balance: Towards a more nuanced conversation about access to beneficial ownership information”, Open Ownership, 18 October 2023, https://www.openownership.org/en/blog/striking-a-balance-towards-a-more-nuanced-conversation-about-access-to-beneficial-ownership-information/.
[58] See, for instance: CJEU, “Opinion of Advocate General Norkus”, 18 December 2025, https://infocuria.curia.europa.eu/tabs/document?source=document&text=&docid=307277&pageIndex=0&doclang=EN&mode=lst&dir=&occ=first&part=1&cid=7510469.
[59] GDPR Hub, “VfGH - E2189/2025”, 21 January 2026, https://gdprhub.eu/index.php?title=VfGH_-_E2189/2025&mtc=today.
[60] Official Journal of the European Union, “Directive (EU) 2024/1640”.
[61] Pinsent Masons, “Ireland limits public access to register of beneficial owners”, 27 June 2023, https://www.pinsentmasons.com/out-law/news/ireland-limits-public-access-to-register-of-beneficial-owners.
[62] CVR Virk, “CVR - Det Centrale Virksomhedsregister”, n.d., https://datacvr.virk.dk/artikel/system-til-system-adgang-til-cvr-data; INPI, “Liste des pièces justificatives devant accompagner le formulaire de demande d’accès aux données des bénéficiaires effectifs pour les personnes assujetties ou justifiant d’un intérêt légitim”, n.d., https://www.inpi.fr/sites/default/files/2026-01/Liste%20des%20pi%C3%A8ces%20justificatives.pdf.
[63] Erhvervsstyrelsen, “Adgang til oplysninger om reelle ejere”, 25 August 2025, https://erhvervsstyrelsen.dk/vejledning-adgang-til-oplysninger-om-reelle-ejere; INPI, “Demande d’accès aux données des bénéficiaires effectifs (BE)”, https://data.inpi.fr/content/editorial/acces_BE.
[64] Central Bank of Ireland, “Access the Beneficial Ownership Register”, 9 April 2026, https://www.centralbank.ie/regulation/anti-money-laundering-and-countering-the-financing-of-terrorism/beneficial-ownership-register.
[65] UNODC, “Reference document on good practices, challenges and lessons learned with respect to beneficial ownership transparency”, CAC/COSP/WG.2/2024/2, 3 April 2024, https://track.unodc.org/uploads/documents/UNCAC/WorkingGroups/workinggroup2/2024-June-10-14/CAC-COSP-WG.2-2024-2/2406076E.pdf; UNODC, “Outcome of the Intergovernmental Meeting on Enhancing the Use of Beneficial Ownership Information to Strengthen Asset Recovery”, CAC/COSP/WG.4/2025/CRP.2, 13 June 2025, https://track.unodc.org/uploads/documents/UNCAC/WorkingGroups/workinggroup4/2025-June-17-20/CRP.2/CAC-COSP-WG.4-2025-CRP.2_E.pdf.
[66] See: “Box 2: The role of data intermediaries in filling current gaps to access and process beneficial ownership information” in Rialet, Understanding beneficial ownership data use, 14.
[67] Rialet, Understanding beneficial ownership data use.
[68] UNODC, “Reference document on good practices, challenges and lessons learned with respect to beneficial ownership transparency”, CAC/COSP/WG.2/2024/2, 3 April 2024, https://track.unodc.org/uploads/documents/UNCAC/WorkingGroups/workinggroup2/2024-June-10-14/CAC-COSP-WG.2-2024-2/2406076E.pdf.
[69] UK government, Home Office, Statutory review of the implementation of the exchange of notes on beneficial ownership between the United Kingdom, Crown Dependencies and Overseas Territories (Home Office, 2019), https://www.gov.uk/government/publications/statutory-review-of-the-exchange-of-notes-arrangements/statutory-review-of-the-implementation-of-the-exchange-of-notes-on-beneficial-ownership-between-the-united-kingdom-crown-dependencies-and-overseas-te.
[70] European Union Agency for Criminal Justice Cooperation, “Joint investigation teams”, n.d., https://www.eurojust.europa.eu/judicial-cooperation/instruments/joint-investigation-teams.
[71] Official Journal of the European Union, “Directive (EU) 2024/1640”, Article 12.
[72] e-Justice, “Beneficial ownership registers interconnection system (BORIS)”, n.d., https://e-justice.europa.eu/topics/registers-business-insolvency-land/beneficial-ownership-registers-interconnection-system-boris_en.
[73] Open Ownership, Usable beneficial ownership data.
[74] Open Ownership, Usable beneficial ownership data.
[75] UK government, Department for Levelling Up, Housing & Communities, Department for Business & Trade, HM Treasury, and HM Revenue & Customs, “Closed consultation: Transparency of land ownership involving trusts”, 27 December 2023, https://www.gov.uk/government/consultations/transparency-of-land-ownership-involving-trusts-consultation/transparency-of-land-ownership-involving-trusts.
[76] See: Kadie Armstrong and Stephen Abbott Pugh, Using reliable identifiers for corporate vehicles in beneficial ownership data (Open Ownership, 2023), https://www.openownership.org/en/publications/using-reliable-identifiers-for-corporate-vehicles-in-beneficial-ownership-data/.
[77] FATF, “Recommendation 24” in FATF Recommendations, 96.
[78] Miranda Evans, “Lessons from building a prototype single-search tool for beneficial ownership registers”, Open Ownership, 7 March 2025, https://www.openownership.org/en/blog/lessons-from-building-a-prototype-single-search-tool-for-beneficial-ownership-registers/; Rialet Understanding beneficial ownership data use.
[79] See, for example the UK: UK government, Transparency and Trust, 8.
[80] GLEIF, “The Legal Entity Identifier (LEI)”, n.d, https://www.gleif.org/en/organizational-identity/lei-vlei/the-legal-entity-identifier-lei; International Organization for Standardization, “ISO 3166 –Country Codes”, n.d., https://www.iso.org/iso-3166-country-codes.html; International Organization for Standardization, “ISO 8601 – Date and time format”, n.d., https://www.iso.org/iso-8601-date-and-time-format.html; Open Ownership, “Beneficial Ownership Data Standard v0.4)”, n.d., http://standard.openownership.org/.
[81] Sara Brimbeuf, Maíra Martini, Florian Hollenbach, and David Szakonyi, Behind A Wall: Investigating Company and Real Estate Ownership in France (Transparency International France and Anti-Corruption Data Collective, 2023), 6, https://files.transparencycdn.org/images/2023-Report-Behind-a-Wall-English.pdf.
[82] Brimbeuf et al., Behind a Wall, 32.
[83] Maria Jofre and Tymon Kiepe, “A brief assessment of the usability of Norway’s beneficial ownership register”, Open Ownership, 24 November 2025, https://www.openownership.org/en/blog/a-brief-assessment-of-the-usability-of-norways-beneficial-ownership-register/.
[84] Baltazar and Manuel, Beneficial Ownership Data Use Research Report.
[85] For example, investigative journalists are sometimes threatened, harmed, and murdered as a result of their investigations. See: Carmen Molina Acosta, “‘It is still dangerous to be a journalist’: Daphne Caruana Galizia’s son reflects on her life and legacy”, International Consortium of Investigative Journalists, 12 January 2024, https://www.icij.org/investigations/panama-papers/it-is-still-dangerous-to-be-a-journalist-daphne-caruana-galizias-son-reflects-on-her-life-and-legacy/.
[86] AMLD6, Article 12.
[87] Government of the Virgin Islands, Ministry of Financial Services, Economic Development and Digital Transformation, “Policy on Rights of Access to the Register of Beneficial Ownership for BVI Business Companies and Limited Partnerships”, 2025, 4, https://bvi.gov.vg/sites/default/files/policy_on_rights_of_access_to_the_register_of_beneficial_ownership_-_june_2025.pdf.
[88] INPI, “Conditions générales d’utilisation applicables aux comptes permettant l’accès aux données relatives aux bénéficiaires effectifs”, n.d., https://www.inpi.fr/sites/default/files/CGU_acc%C3%A8s_donn%C3%A9es_BE.pdf.
[89] Erhvervsstyrelsen, “Kapitel 3: Må oplysninger om reelle ejere videregives?” in Vejledning om Adgang til oplysninger om reelle ejere (Erhvervsstyrelsen, 2025), https://erhvervsstyrelsen.dk/vejledning-adgang-til-oplysninger-om-reelle-ejere#chapter3.
[90] European Union, “Opinion of Advocate General Pitruzzella”, 20 January 2022, https://eur-lex.europa.eu/legal-content/en/TXT/?uri=CELEX:62020CC0037.
[91] UK government, Home Office, Department for Business & Trade, HM Treasury, Ministry of Justice, Serious Fraud Office, “Supplementary ECHR memorandum: amendments made to parts 1-3 Economic Crime and Corporate Transparency Bill (BEIS measures)”, updated 26 October 2023, https://www.gov.uk/government/publications/economic-crime-and-corporate-transparency-bill-2022-echr-memoranda/supplementary-echr-memorandum-amendments-made-to-parts-1-3-economic-crime-and-corporate-transparency-bill-beis-measures.
[92] Government of Kenya, “Executive Order No. 2 of 2018”. At the time of writing, the Kenyan Revenue Authority had an API connection to BO information, and one with the Public Procurement Regulatory Authority was under discussion.
[93] While this is technically not information from the central register but separately collected, the PPRA and BRS are working on an integration.
[94] Government of the Philippines, “Republic Act No. 12253”, 5 September 2025, https://www.officialgazette.gov.ph/2025/09/05/republic-act-no-12253/.
[95] Republic of the Philippines, “New Government Procurement Act (Republic Act No. 12009)”, Government Procurement Policy Board, https://www.gppb.gov.ph/new-government-procurement-act-republic-act-no-12009/.
[96] Philippines Securities and Exchange Commission, “SEC MC No. 15”.
[97] Official Journal of the European Union, “Directive (EU) 2024/1640”.
[98] Rialet, Understanding beneficial ownership data use, 14.
[99] UK government, Companies House, “Guidance: Companies House fees”, 1 February 2026, https://www.gov.uk/government/publications/companies-house-fees/companies-house-fees#bulk-fee.
[100] UK government, Companies House, “Changes to Companies House fees", 1 February 2026, https://changestoukcompanylaw.campaign.gov.uk/changes-to-companies-house-fees/.
[101] Open Ownership’s guide to drafting effective legislation for BOT provides more detailed guidance on best practices for effective legislation, including country examples. See: Ime and Kiepe, Guide to drafting effective legislation for beneficial ownership transparency.